 19
19  19
19  11
11  11
11  5
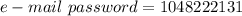
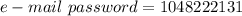
5 Her e-mail password is 
Step-by-step explanation:
You know that a part of Rivka's e-mail password is formed by the last four digits of her telephone number.
The exercise gives you the last four digits of Rivka's telephone number:

Now, in order to find the other numbers, you need to descompose  into its prime factors. Then:
into its prime factors. Then:

Therefore, based on this, you can determine that her e-mail password is:
 5
5 Her e-mail password is 
Step-by-step explanation:
You know that a part of Rivka's e-mail password is formed by the last four digits of her telephone number.
The exercise gives you the last four digits of Rivka's telephone number:

Now, in order to find the other numbers, you need to descompose  into its prime factors. Then:
into its prime factors. Then:

Therefore, based on this, you can determine that her e-mail password is:
 33
33 a. phishing.
Explanation:
According to my research on information technology and cyber-crimes, I can say that based on the information provided within the question this e-mail was an example of phishing. This is a cyber-crime where an individual receives an e-mail, phone call, or text message claiming to be an official authoritative agency in order to trick the individual into releasing private and personal information that they can steal. Which is what is happening to Ivanov by receiving the fake e-mail, if he would have entered in his account information that info would have gone to the people who created the cyber attack.
I hope this answered your question. If you have any more questions feel free to ask away at .
a. phishing.
Explanation:
According to my research on information technology and cyber-crimes, I can say that based on the information provided within the question this e-mail was an example of phishing. This is a cyber-crime where an individual receives an e-mail, phone call, or text message claiming to be an official authoritative agency in order to trick the individual into releasing private and personal information that they can steal. Which is what is happening to Ivanov by receiving the fake e-mail, if he would have entered in his account information that info would have gone to the people who created the cyber attack.
I hope this answered your question. If you have any more questions feel free to ask away at .
 33
33 
It will provide an instant answer!
